Least Trust Lean Function (LTLF) Strategy
We feel confident getting in front our client’s auditors and regulators because we design IT to protect data. By allowing minimal access to data (least trust) and by limiting the software and systems in your company that can store that data (lean function), you can dramatically lower the size of the attack surface area for attackers and simplify cybersecurity. There are less places to store customer data, less places to access that data, and fewer people with the access to the data. Least Trust Lean Function is the core strategy of the Inquisitive IT offering

Right Data
Right person
Right level of access
Right time
Right reason

Least Trust
Least Trust Access is also know as Zero Trust (ZT). The strategy is to start with no access and give employees the minimum amount of access to resources and data so that in the event of a breach, the attacker cannot move laterally throughout the company. This minimizes damage similar to a ship with multiple compartments resilient to sinking. Historically its easier to give access to all employees, but this exposes the entire company to data breach in an attack
Together with our clients, we can assist in policies snd enforcement of a Least Trust strategy. Controls and tools that might assist and enforce Least Trust include: regular access reviews, IAM (Identity Access Management) tools, data discovery and classification, employee granting and exit policies, file de-duplication, data retention policies, and limited sanctioned file sharing tools (Google Drive, Sharepoint, Dropbox, etc)
Lean Function
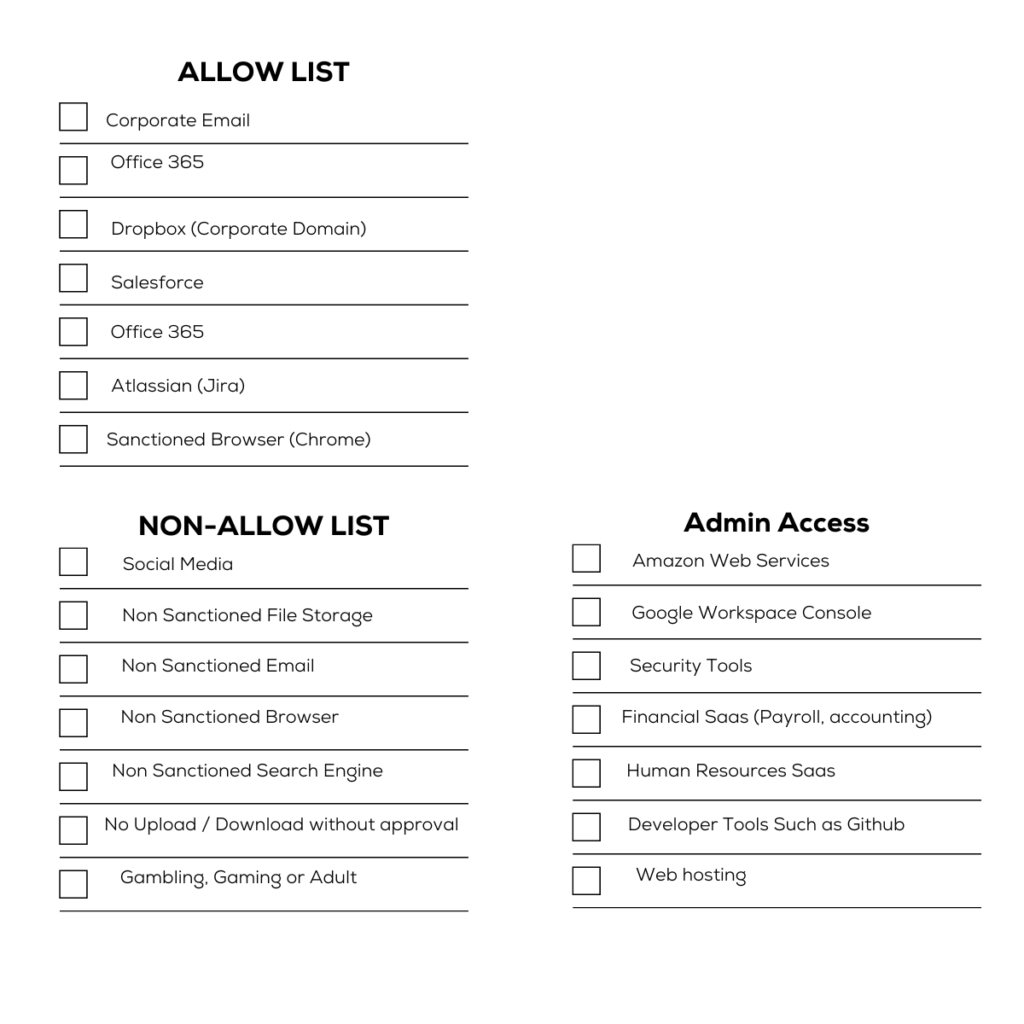
By limiting the places you can store sensitive data, you limit the areas you need to secure. Additionally, businesses can govern and monitor the flow of data throughout the enterprise by providing discrete access to IT that is appropriate for the employees roles and responsibilities. We call this sanctioned IT (Allow List) vs non-sanctioned (Non-allowed List) IT.
- Halt access to websites that might be detrimental to the company (Malware, HR violations, data sharing)
- Restrict sensitive tools and data access to Financial & HR Systems
- Reveal metrics on paid software utilization and performance (rationalize software spend)
- Deter insider Intellectual Property (IP) theft
- Foster security culture & solicit feedback from employees on adding Allowlist (Whitelisting) new software and services
- Reduce 3rd party software risk by working with and auditing fewer providers
- Evidence to auditors, regulators, and outside stakeholders compliance to the law (Where is the customer’s data? Who has access? How might that data flow outside the organization?)
IT Transparency
By switching to Least Trust & Lean Function, your organization gains compliance visibility, IT and employee insights, greater security, lower risk, and cost efficiencies
Nationwide Coverage
Our Team is located across the United States and can respond to your needs virtually in real time or be on location in hours.